Last week, I entered a course at Mälardalens Högskola (MdH, soon to be MdU) in cyber security, more specifically DVA486 – Fundamentals of Industrial Cybersecurity. The course consists of lectures, webinars and assignments that so far has been in the form of written reports. With most of my writing time having to be spent on the course, the best I can offer this blog right now are these assignment reports, with some sprinkles on top. For last week’s assignment, I chose to write about ransomware attacks targeting the healthcare sector. So without further ado, here it is!
Cyber attacks in the healthcare area have become prevalent in recent years. The combination of technology’s role in healthcare as a means of treating patients and underbudgeted IT infrastructure has made hospitals a lucrative target for cyber attackers. A common type of attack against the healthcare industry is ransomware attacks. This report describes the properties of recent ransomware attacks against the healthcare sector and their consequences.
Ransomware
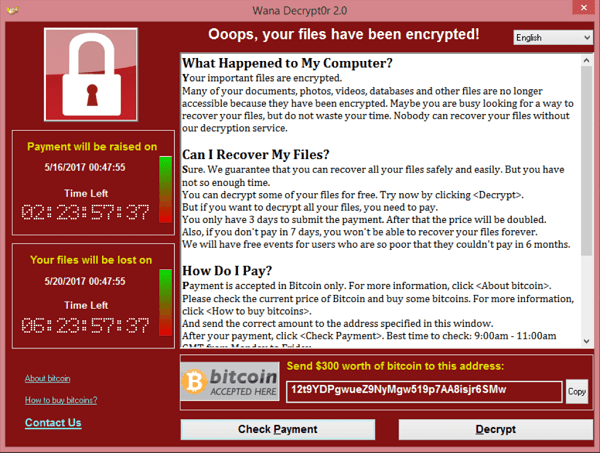
Software known as ransomware is a type of malicious software that uses cryptography to make the victim’s computer system inaccessible until a ransom is paid. In practice, the ransomware may for instance encrypt a user’s files and demand a certain amount of money to be transferred using a bitcoin wallet. Notable examples of ransomware software are WannaCry and Petya.
Comparitec reported that ransomware attacks cost the healthcare industry $20.8 billion in 2020 and observed 92 individual ransomware attacks on healthcare organizations, more than double the number in 2019. [1]
In a survey report from CyberMDX and Philips [2], the results showed that while a majority of healthcare institutions had experienced shutdowns of the computer systems in recent times due to cyber attacks, only 11% of the respondents said that cyber security is a high priority in terms of budgeting.
Countermeasures
In an attack on the 14th of May, 2021, a major ransomware cyber attack targeted the Health Service Executive of Ireland which caused all of its IT systems nationwide to be shut down. While other healthcare organizations may see no other way than paying the ransom or patient safety is at risk, the response from Taoiseach (Ireland’s prime minister) Micheál Martin was to not pay any ransom and instead deal with the attack in a “methodical way” [3]. The Irish defence forces deployed so called ‘ethical hackers’ who fought back against the attack by analyzing the malware, looking for hidden threats and working on decrypting and getting back the data that was affected [4].
Impact and consequences
While the impact of ransomware attacks on healthcare is often measured in terms of financial losses, a more diffuse factor is the cost of patient health due to disrupted care. A tragic example of this happened in Germany just over a year ago where a woman in need of urgent care was unable to be treated at the closest hospital due to a cyber attack shutting down the system. The woman was sent to a hospital much further away which delayed her treatment and eventually led to her death [5].
The way forward
In a paper by Bhuyan et al [6], several recommendations are presented to deal with cyber security threats. On the policy making level, improvements to laws and regulations such as HIPAA are needed to keep up to date with technology advancements. In relation to that, blockchain has been suggested as a way to make electronic health records more secure. With regards to that, a quote by Bruce Schneier feels close at hand: “If you think technology can solve your security problems, then you don’t understand the problems and you don’t understand the technology.” [7]
As for the healthcare organizations, Bhuyan et al present various processes and frameworks to improve cyber security. In summary, actions across all levels of the organizations, from budget decisions to end user training and education, are required to become better prepared for cyber attacks.
From my personal experience, based on things I’ve heard from people working in the industry, it seems that a common way of thinking is to make the IT equipment and software “work” for as long as possible while spending as little money on it as possible. This can hopefully change without actual ransomware attacks happening, lest it seems like only a matter of time before they will strike.
Sources
[1]: Bischoff, Paul. “Ransomware attacks on US healthcare organizations cost $20.8bn in 2020.” Comparitech, 2021-03-10, https://www.comparitech.com/blog/information-security/ransomware-attacks-hospitals-data/ Accessed: 2021-09-26.
[2]: Ipsos. “Perspectives in Healthcare Security”. Ipsos, 2021-09-09. https://info.cybermdx.com/hubfs/Downloadable Assets/CyberMDX Philips_Perspectives in Healthcare Security Report.pdf Accessed: 2021-09-26.
[3]: Horgan-Jones, Jack et al. “Bitcoin ransom will not be paid following cyber attack on HSE computer systems”. The Irish Times, 2021-05-14, https://www.irishtimes.com/news/health/bitcoin-ransom-will-not-be-paid-following-cyber-attack-on-hse-computer-systems-1.4564957 Accessed: 2021-09-26.
[4]: O’Connor, Niall. “Defence Forces deployed ‘ethical hackers’ to fight back against massive HSE cyber attack”. The Journal, 2021-07-20, https://www.thejournal.ie/defence-forces-cis-how-they-fought-the-hse-cyber-attack-5499730-Jul2021/ Accessed: 2021-09-26
[5]: Associated Press. “German hospital hacked, patient taken to another city dies”. AP News, 2020-09-17, https://apnews.com/article/technology-hacking-europe-cf8f8eee1adcec69bcc864f2c4308c94 Accessed: 2021-09-26
[6]: Bhuyan, Soumitra Sudip, et al. ”Transforming healthcare cybersecurity from reactive to proactive: current status and future recommendations.” Journal of medical systems 44.5 (2020): 1-9.
[7]: Schneier, Bruce. Secrets and lies: digital security in a networked world. John Wiley & Sons, 2015.
Personal thoughts and discussion
While these types of assignments, e.g. the very broadly defined ”Find some of the most recent cyber-attacks in Sweden or some other part of the world and explain their causes, properties, side effects, financial losses, etc.”, ends up being a regurgitation of what others have written with little to no originality* or novel ideas of my own I suppose that it does have quite a few benefits as well. For starters, I do get to practice my writing in English (surprisingly rare these days) and I get to share the news with friends and strangers alike, which could bring awareness to the subject among people who otherwise would have missed it. Also, my biggest takeaway from this assignment is that I learned that the Irish prime minister is called Taoiseach, an old Irish word for ”leader” which isn’t pronounced as one would expect, at all.
Perhaps this report was too basic or boring for some of you, but if you want to read more then the list of sources might be a good starting point. If you want to read less about cyber security on the other hand, then do not fret for there is plenty of material that is unrelated to cyber security that should end up here on the blog in the next couple months or so. Until they, stay safe and healthy! 🙂
* Very loose reference to a scene in Good Will Hunting, but it’s a good scene (and movie): https://www.youtube.com/watch?v=hIdsjNGCGz4